In 2026, the demand for lightning‑fast, reliable microservices delivery has reached new heights. Enterprises now expect continuous deployment cycles that not only compile and test code but also orchestrate rollouts across multiple Kubernetes clusters with minimal human intervention. By combining Jenkins, GitHub Actions, and ArgoCD, you can create a robust, open‑source CI/CD stack that delivers rapid, repeatable microservice deployments while maintaining strict observability and security controls.
1. Architectural Overview
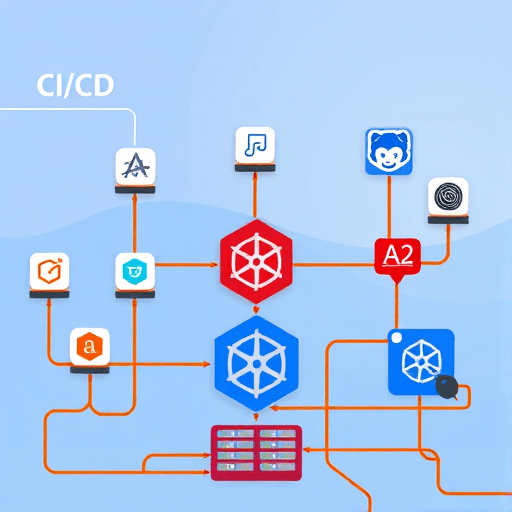
Before diving into tooling, map the high‑level flow:
- Source Control – All microservice code lives in GitHub repositories, with a dedicated branch strategy (main, develop, feature/*).
- Build & Test – Jenkins executes unit, integration, and contract tests, builds Docker images, and pushes them to a trusted container registry.
- PR Validation – GitHub Actions runs lightweight checks (linting, unit tests, security scans) on every pull request.
- Deployment – ArgoCD watches GitOps repositories, applies Helm charts to Kubernetes clusters, and performs canary or blue‑green rollouts.
- Observability – OpenTelemetry traces, Prometheus metrics, and Grafana dashboards surface pipeline health.
- Infrastructure – Terraform provisions cluster nodes, IAM roles, and network policies, while Helm manages microservice manifests.
By separating concerns—source control, build, deployment, and observability—you ensure each tool operates within its strengths and remains easily replaceable if needs evolve.
2. Setting Up Jenkins as the Build Engine
Jenkins continues to thrive as a flexible build orchestrator. In 2026, the Jenkins Kubernetes Plugin automates agent provisioning, reducing build latency. Follow these steps:
- Install Jenkins on a self‑hosted Linux VM or use the Jenkins in Docker image.
- Configure the Kubernetes Plugin: Point Jenkins to the Kubernetes API server of your cluster, specifying a service account with
editrights. This allows Jenkins to spin up build pods on demand. - Create a
Dockerfileanddocker-compose.ymlfor each microservice. The build steps will copy the repo into a Docker context and rundocker build. - Define a Jenkins Pipeline (Jenkinsfile):
pipeline {
agent { label 'docker' }
stages {
stage('Checkout') {
steps { checkout scm }
}
stage('Build') {
steps { sh ‘docker build -t ${IMAGE_NAME}:${GIT_COMMIT} .’ }
}
stage('Test') {
steps { sh ‘mvn test’ }
}
stage('Publish') {
steps { sh ‘docker push ${IMAGE_NAME}:${GIT_COMMIT}’ }
}
}
}
Use image: docker:20.10 in your Jenkins agent pod spec to support multi‑stage builds. Store secrets (registry credentials, API tokens) in Jenkins credentials store and inject them as environment variables.
Why Jenkins Remains Relevant
- Granular control over build stages.
- Rich plugin ecosystem for static analysis, security scanning, and artifact promotion.
- Scalable agent pool via Kubernetes, enabling parallel builds across microservices.
3. Configuring GitHub Actions for Pull‑Request Validation
GitHub Actions now offers first‑class support for GitOps triggers and self‑hosting runners on Kubernetes. Use a lightweight workflow to catch defects early:
name: PR Validation
on:
pull_request:
branches: [ main ]
jobs:
lint:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- name: Install Node
uses: actions/setup-node@v4
with:
node-version: '20'
- name: Lint
run: npm run lint
unit-test:
needs: lint
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- name: Run Tests
run: npm test
container-scan:
needs: unit-test
runs-on: ubuntu-latest
steps:
- uses: aquasecurity/trivy-action@v0.1
with:
image-ref: myrepo/${{ github.repository }}:${{ github.sha }}
format: table
Key points:
- Use
needsto enforce order. - Run
trivyfor vulnerability scanning before the build is triggered in Jenkins. - Leverage
github-tokento comment on PRs automatically.
This PR pipeline provides rapid feedback to developers, reducing merge latency and preventing broken code from entering the CI pipeline.
4. ArgoCD Deployment Workflow
ArgoCD is the centerpiece of GitOps for Kubernetes. It watches a dedicated gitops repository containing Helm charts for each microservice. The workflow:
- Sync Policy: Set
Automaticwith aPruneflag so that deletions in Git propagate to clusters. - Rollout Strategy: Use
CanaryDeploymentorBlueGreenDeploymentvia Argo Rollouts integration. Configure aRolloutmanifest withstrategy.canaryorstrategy.blueGreensections. - Health Checks: Define
HealthChecksandPostSynchooks that wait for readiness probes and custom metrics. - Automatic Promotion: After successful canary rollout and passing Prometheus alerts, ArgoCD can auto‑promote to stable.
Below is an example of a Rollout spec for a microservice:
apiVersion: argoproj.io/v1alpha1
kind: Rollout
metadata:
name: user-service
spec:
replicas: 5
selector:
matchLabels:
app: user-service
template:
metadata:
labels:
app: user-service
spec:
containers:
- name: user-service
image: myrepo/user-service:${{ GIT_COMMIT }}
strategy:
canary:
steps:
- setWeight: 20
- pause: { duration: 5m }
- setWeight: 50
- pause: { duration: 10m }
- setWeight: 100
After deployment, ArgoCD’s UI shows progress, enabling operators to roll back instantly if anomalies surface.
5. Integrating Observability and Security
Observability is not optional; it is the safety net that guarantees deployment reliability.
- OpenTelemetry traces each step in the pipeline. Attach an OTel collector to Jenkins agents to export traces to a collector that forwards to Tempo.
- Prometheus scrapes metrics from Jenkins (build durations, failure rates) and ArgoCD (sync status, sync errors). Use Grafana dashboards that auto‑update.
- Secure Secrets Management with HashiCorp Vault. Jenkins pulls image pull secrets from Vault; ArgoCD uses
argocd-vault-pluginto inject runtime secrets into pods. - Compliance Checks with
kube-benchandkube-hunterrun in a nightly Jenkins job to scan cluster security posture.
6. Automating Infrastructure with Terraform and Helm
Infrastructure-as-Code keeps your clusters reproducible. Terraform provisions VPCs, subnets, IAM roles, and Kubernetes control planes (via aws-eks or azure-aks modules). Helm charts, stored in a separate charts repo, manage microservice manifests. The CI/CD stack pulls the Terraform state to detect drift and automatically triggers terraform apply when changes occur.
- Terraform Workspace per Environment –
dev,staging,prod. - Terraform Cloud Workspace for remote state and policy checks.
- Helm Repository as a GitOps Source – ArgoCD fetches Helm chart versions via
git tagsemantics.
7. Testing Strategies in the Pipeline
Robust testing is critical. In addition to unit and integration tests, implement:
- Contract Tests with Pact to validate microservice interfaces.
- Chaos Engineering in a
canarynamespace usingLitmusChaostriggered by ArgoCD hooks. - Performance Tests with
k6run in a Jenkins pipeline stage. Export results to Grafana. - Use
testcontainersto spin up dependency services (Kafka, PostgreSQL) in Docker during integration tests.
8. Monitoring and Rollback
After deployment, continuously monitor:
- Application health via readiness/liveness probes.
- Service latency and error rates via OpenTelemetry.
- Cluster capacity and node health via
cAdvisorandkube-state-metrics.
ArgoCD’s sync policy: automatic coupled with auto-prune ensures that misconfigurations are rapidly reverted. For manual control, operators can trigger a rollout undo from the ArgoCD UI.
Conclusion
By weaving Jenkins, GitHub Actions, and ArgoCD into a single, open‑source CI/CD fabric, teams can achieve rapid, reliable microservice deployments that scale with their Kubernetes workloads. The approach balances human oversight—through PR validation and manual rollbacks—with automated observability and security, ensuring that every change is tested, monitored, and auditable. As 2026 brings new cloud-native primitives, this pipeline remains modular, allowing future plug‑ins (e.g., serverless triggers, AI‑driven test selection) to slot in with minimal friction.



