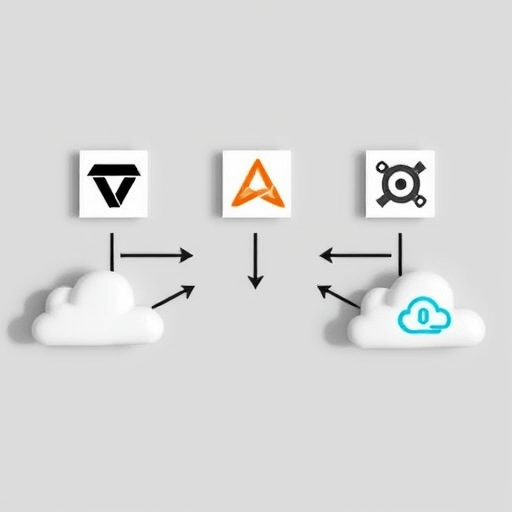
In 2026, organizations are juggling Terraform modules, Ansible playbooks, and a sprawling array of public and private clouds. The question that keeps architects awake at night is: How do we keep Terraform and Ansible configs synced across clouds with Pulumi? This article explores a concrete workflow that merges Terraform state, Ansible automation, and Pulumi’s unified SDK to eliminate drift, streamline CI/CD, and deliver a single source of truth.
The Drift Problem in Multi‑Cloud Ops
When Terraform and Ansible are used side‑by‑side, each tool evolves its own notion of what the infrastructure should look like. Terraform’s state file records resources as declarative objects, while Ansible’s idempotent tasks manipulate resources at runtime. Over time, manual edits, cloud provider updates, or even automated scaling can cause the actual resources to diverge from both configurations. This divergence, known as drift, is especially painful in multi‑cloud environments where API nuances differ, making reconciliation a manual, error‑prone process.
Typical symptoms include:
- Resource IDs changing in the cloud console without corresponding Terraform changes.
- Ansible playbooks reporting “changed” even when the target state is already achieved.
- CI pipelines failing due to mismatched state or missing dependencies.
Without a unified approach, teams spend weeks debugging misaligned configurations, which hampers delivery velocity and increases the risk of outages.
Why Pulumi Bridges Terraform & Ansible
Pulumi extends the infrastructure-as-code model by allowing developers to write provisioning logic in familiar programming languages such as TypeScript, Python, Go, or C#. Its SDK supports Terraform providers through the terraform package and Ansible modules via the ansible package, enabling a single Pulumi stack to reference resources defined elsewhere.
Key advantages of using Pulumi as the glue:
- Unified State Management – Pulumi keeps a single state file that tracks both Terraform and Ansible resources, reducing the chances of conflict.
- Rich Type Checking – Language features (static types, generics) help catch configuration errors before deployment.
- Cross‑Provider Composition – You can define a network in Terraform, provision a VM with Ansible, and tie them together in Pulumi, ensuring that all components are orchestrated atomically.
- Policy as Code – Pulumi supports OPA or custom policies that can enforce naming conventions or compliance rules across Terraform and Ansible resources.
In essence, Pulumi becomes the orchestrator that reconciles the declarative world of Terraform with the imperative logic of Ansible, keeping both in sync across any number of cloud environments.
Setting Up Pulumi to Import Existing Terraform State
Before Pulumi can sync Terraform configurations, it must ingest the current Terraform state. The process is straightforward but requires attention to detail to avoid state corruption.
- Backup Your State – Store a copy of each
terraform.tfstatein an object storage bucket or an S3-compatible service. - Install the Pulumi Terraform Provider – In your Pulumi project, add the Terraform provider for the cloud you are targeting, e.g.
npm install @pulumi/terraform. - Create a Pulumi Stack – Run
pulumi newand choose a language template. Initialize the stack withpulumi stack init prod. - Import State – Use Pulumi’s
terraform.importfunction to read the Terraform state into Pulumi. Example in TypeScript:
import * as terraform from "@pulumi/terraform";
const tfState = terraform.import({
provider: "aws",
stack: "prod",
state: "s3://my-terraform-states/prod.tfstate",
});
After importing, Pulumi’s state file will contain references to all Terraform resources. From this point forward, any changes to the infrastructure should go through Pulumi, which will translate them back to Terraform’s format.
Syncing Ansible Playbooks Through Pulumi
While Pulumi can import Terraform state, synchronizing Ansible playbooks requires a slightly different approach. Pulumi’s ansible package allows you to run Ansible tasks as part of the provisioning flow, ensuring that the same state is represented in both tools.
- Bundle Ansible Roles – Keep your playbooks in a dedicated directory (e.g.,
ansible/) and package them into a Docker container if they depend on external binaries. - Define Ansible Resources – In your Pulumi code, create an Ansible resource that references the playbook. For example, in Python:
from pulumi_ansible import AnsibleResource
deploy_web = AnsibleResource("deployWeb",
playbook="ansible/web_server.yml",
inventory="ansible/inventory/production",
options={"become": True}
)
This Ansible resource becomes part of Pulumi’s state. When you run pulumi up, Pulumi first ensures that the Terraform resources are provisioned and then executes the Ansible playbook against the target hosts.
Because Pulumi tracks the outputs of the Ansible run, you can reference them later in Terraform modules. For example, a Terraform module that needs the IP address of a web server can pull that value from the Ansible resource’s output.
Advanced Patterns: State‑Management, CI/CD, and Policy as Code
To achieve truly drift‑free infrastructure, teams must embed best practices into their pipeline. Pulumi’s SDK makes it simple to implement these patterns.
- Remote State Backend – Store Pulumi state in a locked, encrypted backend (e.g., Pulumi Service or an S3 bucket with DynamoDB locks). This ensures that concurrent deployments are serialized.
- CI/CD Integration – Add Pulumi steps to your GitHub Actions or GitLab CI pipeline. A typical job might run
pulumi previewto show a diff, followed bypulumi up --yeson merge tomain. - Automated Drift Detection – Schedule a nightly
pulumi refreshto compare the real infrastructure against Pulumi’s state. Any differences are surfaced as drift and can trigger alerts. - Policy as Code – Use Pulumi’s policy framework to enforce constraints across Terraform and Ansible. For instance, a policy that forbids any resource lacking a specific tag or a rule that mandates an Ansible role be present whenever a Terraform module creates an EC2 instance.
- Cross‑Cloud Identity Mapping – When resources span multiple clouds, use Pulumi’s output forwarding to propagate provider credentials and resource identifiers between stacks. This eliminates manual copy‑paste and reduces errors.
Real‑World Use Case: A 2026 Global E‑Commerce Platform
Consider ShopAll, a global e‑commerce startup that runs its front‑end in AWS, its data lake in Azure, and its Kubernetes cluster in Google Cloud. Historically, the team used Terraform for networking and Azure resources, while Ansible managed VM configuration and Kubernetes deployment. Whenever a new microservice was added, developers would:
- Update Terraform modules for the networking layer.
- Edit an Ansible role to bootstrap the service.
- Push changes to separate Git repositories, triggering distinct CI pipelines.
- Manually merge state snapshots into a central monitoring dashboard.
In 2026, the company adopted Pulumi to unify these steps:
- Single Repository – All Terraform modules, Ansible playbooks, and Pulumi code live in one repo, tagged by environment (dev, staging, prod).
- Unified Stack – A
shopall-prodPulumi stack imports AWS networking state, Azure data lake state, and Google Kubernetes state. - Automated Deployment – A GitHub Actions workflow runs
pulumi previewto detect infra changes. If differences exist, the workflow automatically runspulumi upafter merging, ensuring that both Terraform and Ansible remain in sync. - Drift Prevention – The pipeline schedules nightly
pulumi refreshruns. Any drift triggers a Slack notification, and the pipeline can automatically re‑apply the desired state.
Result: ShopAll reduced deployment time from days to hours, eliminated manual state reconciliation, and achieved a 40% reduction in infrastructure-related incidents.
Conclusion
By leveraging Pulumi as a bridge between Terraform and Ansible, teams can maintain a single, consistent source of truth across multiple clouds. The approach consolidates state, enforces policies, and integrates seamlessly into modern CI/CD pipelines, providing a robust foundation for drift‑free infrastructure in 2026 and beyond.