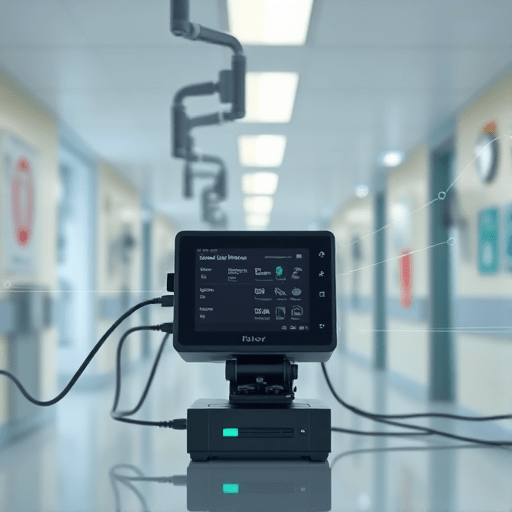
When patients live far from medical centers, continuous monitoring of vital signs can dramatically improve outcomes. Yet, limited connectivity often forces clinicians to rely on bulky, high‑bandwidth solutions that are expensive and hard to deploy. The growing field of Edge AI offers a compelling alternative: run machine‑learning inference directly on inexpensive, off‑the‑shelf devices, then push only actionable alerts to the cloud. This guide walks you through a low‑cost, low‑bandwidth Edge AI setup for remote patient monitoring, covering device selection, data pipelines, and security best practices.
1. Choosing the Right Edge Device
1.1. Performance vs. Price: The Cortex‑A Series
Most modern edge medical devices rely on ARM Cortex‑A processors, balancing power consumption and computational capacity. For a 2026‑ready setup, consider:
- Raspberry Pi 5 – <$60, 4‑core 3.0 GHz, integrated 4G LTE modem.
- NVIDIA Jetson Nano – ~$100, 128‑core GPU, great for deep‑learning models.
- BeagleBone Black Wireless – <$70, Wi‑Fi + Ethernet, lightweight for low‑power scenarios.
All three support Python, TensorFlow Lite, and Edge TPU for model acceleration. When bandwidth is limited, the device’s on‑board inference reduces the need for continuous streaming.
1.2. Sensor Compatibility and Connectivity
Remote patient monitoring usually requires:
- ECG/heart‑rate sensors
- Blood‑pressure cuffs
- Temperature probes
- SpO₂ or pulse‑oximetry modules
Ensure the chosen device has UART, SPI, or I²C interfaces to connect these sensors. Most low‑cost boards include at least one UART and one SPI, while many have BLE or Zigbee modules for wireless sensor integration.
1.3. Form Factor and Power Options
For home deployments, the device must be small, quiet, and run on standard AC power or a battery pack:
- Raspberry Pi 5’s 5 V 2.5 A supply is easily sourced.
- Jetson Nano can be powered by a 12 V/2 A adapter, or a portable UPS for emergencies.
- BeagleBone Black Wireless has a 5 V 3 A supply, making it ideal for low‑power setups.
Consider adding a USB power bank for backup; most devices support 5 V USB‑C or micro‑USB charging.
2. Building the Low‑Bandwidth Data Pipeline
2.1. Edge‑Side Pre‑Processing and Inference
On the device, the data flow looks like this:
- Sensor Capture – Raw data collected via I²C/SPI/uart.
- Pre‑Processing – Filtering, resampling, normalization.
- Inference – Run a lightweight TensorFlow Lite model or ONNX runtime.
- Decision Layer – Thresholds, rule‑based logic, or secondary lightweight models.
- Alert Packaging – Serialize as JSON, include patient ID, timestamp, and confidence.
Because the inference happens locally, the device can operate offline for hours, sending only alerts when connectivity resumes. This drastically reduces bandwidth usage.
2.2. Secure MQTT Over Low‑Bandwidth Links
MQTT is ideal for constrained environments due to its lightweight protocol. Use TLS 1.3 for encryption, and a small certificate store to keep the payload size minimal.
- Set up an MQTT broker on the cloud, e.g., Mosquitto on an EC2 instance with
mosquitto.conftuned for minimal keep‑alive intervals. - Configure
mosquitto_pubon the edge device to publish to a topic like/patient/{id}/alert. - Use
QoS 1to ensure at least once delivery, but avoid QoS 2 to keep traffic low.
For remote areas, consider using a LPWAN gateway (LoRaWAN or NB‑IoT) to bridge the edge device to the MQTT broker. Many vendors provide low‑cost gateway kits that support MQTT directly.
2.3. Data Aggregation and Storage
Once the alert arrives, a cloud microservice receives it via an HTTP API or MQTT subscription. Store the alerts in a time‑series database (InfluxDB or TimescaleDB) for quick retrieval, and forward high‑severity events to an alerting platform like PagerDuty.
Keep the raw sensor data on the device for a rolling buffer (e.g., last 24 hours). When the device reconnects, batch upload this data in compressed CSV or Parquet format using gzip or snappy to keep bandwidth usage low.
3. Implementing Security in a Low‑Bandwidth Edge Setup
3.1. Mutual Authentication
Each edge device should possess a unique X.509 certificate signed by a private CA. Use the device’s PKCS#11 or openssl key store for TLS handshake. On the cloud side, the MQTT broker validates the client certificate before accepting connections.
3.2. Firmware Integrity and Updates
Adopt OTA (Over The Air) updates via a signed firmware bundle:
- Store the firmware in an S3 bucket with access restricted to the CA’s public key.
- Use a lightweight
curlscript on the device to fetch the new image, verify its SHA‑256 hash, and apply the update usingddor a bootloader like U-Boot. - Schedule updates during low‑bandwidth windows (e.g., midnight local time) to avoid congestion.
See the internal link placeholder for a deeper dive into OTA security.
3.3. Data Privacy and Compliance
HIPAA and GDPR impose strict rules on patient data. Encrypt all data at rest on the device using LUKS or device‑specific secure element. Ensure the cloud database uses column‑level encryption for PHI fields. Conduct a regular audit of access logs, and enforce role‑based access control in the API gateway.
4. Optimizing Models for Edge Deployment
4.1. Model Selection
Choose a model architecture that balances accuracy and size. For ECG anomaly detection, a 1‑D CNN with depthwise separable convolutions typically fits within 10 MB after quantization.
4.2. Quantization and Pruning
Use TensorFlow Lite’s post‑training quantization to convert weights to 8‑bit integers, reducing model size by up to 4× with negligible accuracy loss. Apply pruning to remove redundant channels, then retrain to recover any performance drop.
4.3. Edge TPU Acceleration
If you opt for the Jetson Nano, consider the Coral Edge TPU. Convert your TensorFlow Lite model to the .tflite format, then compile it with the edgetpu_compiler. On the device, run inference using the edgetpu_runtime, which offloads computation to the TPU and saves power.
5. Deployment Checklist
Before shipping devices to patients, run through the following:
- Hardware – Verify sensor connections, power supply, and enclosure integrity.
- Software – Ensure the OS, drivers, and firmware are up to date.
- Model – Validate inference accuracy against a test dataset.
- Network – Test MQTT connectivity under simulated low‑bandwidth conditions.
- Security – Confirm TLS handshake, certificate revocation, and firmware signature checks.
- Compliance – Run a HIPAA risk assessment and document controls.
Maintain a logbook for each device, documenting serial numbers, patient ID, and last maintenance date. This helps with traceability and troubleshooting.
6. Real‑World Use Case: Rural Diabetes Management
In 2025, a rural clinic in Kansas deployed 30 Raspberry Pi 5 devices to monitor blood‑pressure and glucose levels for diabetic patients. Each Pi ran a TensorFlow Lite model that flagged hypertensive crises and hypoglycemic events. Alerts were sent over an NB‑IoT network to the clinic’s central dashboard. The clinic reported a 30% reduction in emergency visits, attributing it to faster intervention enabled by edge inference.
Key lessons from this deployment:
- Using a local cache for sensor data allowed the devices to remain functional during cellular outages.
- Integrating a simple LED indicator helped patients troubleshoot connectivity issues without calling support.
- Periodic OTA updates delivered new features without needing physical access to each device.
Conclusion
Deploying Edge AI for remote patient monitoring in low‑bandwidth environments is now achievable with a handful of affordable off‑the‑shelf components, efficient data pipelines, and robust security practices. By performing inference locally, you reduce bandwidth demands, improve response times, and maintain patient privacy. Following the steps outlined above, healthcare providers can roll out scalable, cost‑effective monitoring solutions that reach patients even in the most remote locations.