Modern observability pipelines generate terabytes of log data each day.
Scaling log retention on the fly—without incurring service interruptions or
re‑ingesting data—has become a critical capability for high‑volume
organizations. This article explores the architecture, tooling, and best
practices for implementing Zero‑Downtime Log Retention with Dynamic TTLs, a strategy that lets you adjust how long each log
entry lives in storage while keeping costs predictable.
Why Dynamic TTLs Matter in 2026
In 2026, multi‑cloud environments and compliance requirements such as
GDPR, CCPA, and the new Data Retention Simplification Act force teams to
balance archival depth against budget constraints. Static retention
policies—e.g., “store all logs for 30 days”—can quickly become
inflexible. Dynamic Time‑to‑Live (TTL) configurations allow you to
refine retention on a per‑service or even per‑label basis in real time,
drastically cutting storage while ensuring that critical audit trails
remain available.
Core Concepts and Terminology
- TTL (Time‑to‑Live): The duration a log record stays in the store before automatic deletion.
- Retention Policy Engine: A service that interprets policy definitions and applies TTLs to log streams.
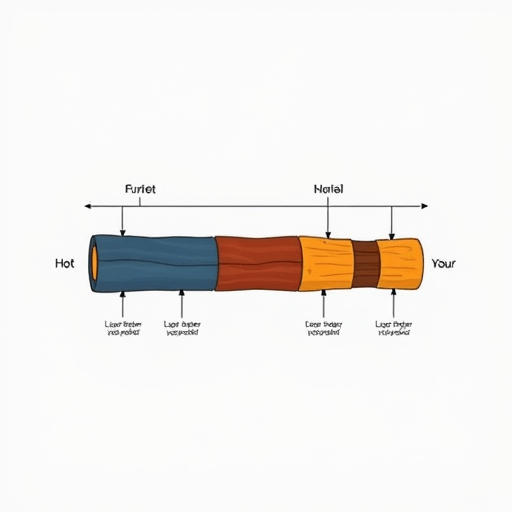
- Hot‑Storage vs. Cold‑Storage: Fast, expensive tiers (e.g., SSD) for recent logs; cheaper, slower tiers (e.g., object storage) for older data.
- Metadata‑Driven Routing: Using tags or labels on log entries to determine their retention path.
Architectural Blueprint for Zero‑Downtime Retention
The goal is to create a pipeline that can shift log entries between
storage tiers or adjust TTLs without stopping ingestion or querying.
A typical production‑grade setup consists of the following layers:
1. Log Producer Layer
Application logs, container logs, and infrastructure metrics are emitted
via a structured format (JSON or OCI log format). Each record should
include a service field, environment tag, and a level indicator. These tags drive later
routing decisions.
2. Ingestion and Normalization
Use a high‑throughput, horizontally scalable log shipper (e.g., Fluent
Bit, Logstash, or a custom Kafka connector). The shipper normalizes
timestamps, injects ingestion time, and forwards records to a
dedicated retention orchestrator.
3. Retention Orchestrator
At the heart of zero‑downtime retention lies the orchestrator—a
microservice that reads policy snapshots from a central config store
(e.g., Consul or etcd), calculates TTLs per log stream, and writes
metadata to the storage layer. It watches for policy changes via
watch APIs and pushes updates to the storage tier without halting
traffic.
4. Storage Tiers
Deploy a two‑tier system:
- Hot Tier: Managed by an Elasticsearch cluster or OpenSearch,
optimized for real‑time search and analytics. - Cold Tier: Amazon S3 Glacier Deep Archive, Azure Blob Cool, or
Google Cloud Storage Nearline, coupled with an object‑based index
(for example, via OpenSearch’sremotefeature).
When a log record ages beyond its TTL in the hot tier, the orchestrator
moves it to cold storage. The move is an idempotent operation, so
re‑runs are harmless.
5. Query Layer
All queries funnel through a single API that abstracts storage
details. It uses a search context to decide whether to query hot
or cold tiers based on the requested time window and a cache hint.
This layer ensures users experience no latency spike when the policy
shifts logs between tiers.
Implementing Dynamic TTL Policies
Dynamic TTLs rely on declarative policy definitions written in a
human‑readable format such as YAML or JSON. Below is an example policy
file:
{
"policies": [
{
"match": {"service": "auth", "environment": "prod"},
"ttl": "90d",
"cold_tier": "archive",
"hot_tier": "search"
},
{
"match": {"service": "payment", "environment": "prod"},
"ttl": "30d",
"cold_tier": "archive",
"hot_tier": "search"
},
{
"match": {"level": "debug"},
"ttl": "7d",
"cold_tier": "archive",
"hot_tier": "search"
}
]
}
The orchestrator parses the policy and computes a record_expiry
timestamp for each incoming log entry. It also attaches a
storage_target tag indicating whether the record belongs in hot or
cold storage.
Rolling Policy Updates Without Downtime
When you need to adjust TTLs—for instance, extending the retention
for the payment service from 30 to 60 days—simply update the policy
file and push it to the config store. The orchestrator’s watch
mechanism detects the change, triggers a reconciliation loop, and
writes new expiry metadata to the hot tier. Existing records
automatically adopt the new TTL if they are still within the hot tier.
Records already in cold storage will remain untouched until they are
eligible for a move back to hot storage (if a reverse TTL change occurs).
Handling Edge Cases: Bursty Traffic and High‑Throughput Streams
- Backpressure: If the orchestrator cannot keep up with ingestion,
introduce a buffer queue (e.g., Kafka or Pulsar). The queue can
store records temporarily while maintaining order. - TTL Drift: To prevent TTL drift in long‑running services,
include apolicy_versionfield. The orchestrator can then
re‑process expired records that were written under an outdated policy. - Compliance Snapshots: For regulated industries, keep a
“snapshot” of the policy at the time a log entry was created. This
allows you to reconstruct the original retention behavior if needed.
Cost Optimisation Strategies
Dynamic TTLs unlock several avenues for cutting storage spend:
1. Intelligent Tiering
By moving logs to cold storage as soon as they exceed their TTL,
you free up expensive hot‑tier capacity. In 2026, many cloud
providers now offer object‑storage tiering APIs that can automate
this transition. Coupled with the orchestrator, this reduces
maintenance overhead.
2. Multi‑Label Retention Granularity
Instead of a blanket 30‑day policy, apply shorter TTLs to
non‑critical data (e.g., debug logs) and longer TTLs to audit logs.
This fine‑grained approach can save up to 40% on storage without
impacting observability.
3. Spot and Pre‑emptible Instances for Cold Tier Indexing
Cold storage indexing—creating searchable metadata for archived logs—can
be performed on spot instances or pre‑emptible VMs. Because the data is
durable in object storage, you can tolerate interruption without data loss.
Monitoring and Alerting the Retention Pipeline
A robust monitoring stack is essential to ensure that TTL policies
are enforced correctly and that logs aren’t inadvertently lost. Key
metrics include:
- Record Lifespan Distribution: Histogram of how long records stay in hot storage.
- Reconciliation Lag: Time between policy update and full enforcement.
- Cold Tier Throughput: Number of records moved to or from cold storage per minute.
- Error Rates: Failed moves, expired record counts, or missing policy matches.
Set alerts on thresholds that could indicate storage cost overruns
or compliance violations. For example, if records_in_hot_tier exceeds
the budgeted capacity by 10%, trigger an alert to review TTL settings.
Case Study: FinTech Co. Reduces Log Costs by 35%
FinTech Co., a payment processor with 5 million logs per day, had
been paying $0.02 per GB in hot storage. By introducing dynamic TTLs
and moving 70% of logs to cold storage after 15 days, they reduced
daily hot‑tier usage to 30% of the original volume. Combined with
multi‑label retention (debug logs dropped after 3 days), the company
cut its total log storage bill from $12,000 to $7,800 per month.
Moreover, the policy engine allowed compliance officers to roll
out new audit retention mandates within minutes, ensuring that
regulatory audits could be conducted without service downtime.
Future‑Proofing Your Log Retention Strategy
Emerging trends such as serverless logging, AI‑driven anomaly
detection, and the rise of policy as code frameworks mean that
log retention will become increasingly dynamic. Here are a few
directions to watch:
- Policy-as-Code Repositories: Store policies in Git, allowing
git‑based reviews, versioning, and rollback. - AI‑Driven TTL Adjustments: Machine learning models can predict
when a log is likely to be queried and extend TTLs accordingly. - Edge‑to‑Cloud Log Shipping: Directly ship logs from edge
devices to the orchestrator, reducing latency for real‑time analytics.
Conclusion
Zero‑downtime log retention with dynamic TTLs is no longer a niche
feature—it’s a necessity for any production environment that needs to
balance compliance, performance, and cost. By adopting a policy‑driven
architecture, you can shift log lifecycles on the fly, automatically
tier logs between hot and cold storage, and keep your observability
pipeline resilient. The result? A leaner storage footprint, predictable
billing, and a compliance posture that can adapt as regulations evolve.